We hear a lot about hacking these days, but in fact, hacking is nothing new. Even long before computers existed, people have tried to hack things. The public became aware of hacking as early as 1903 when Marconi’s wireless telegraph was hacked just as the technology’s capabilities were about to be demonstrated to a large crowd gathered at London’s Royal Institution.
Today, hacking has evolved into a wide-ranging web of cybercrime that is hard to avoid, with perpetrators carrying out their misdeeds for a variety of motives – selling data for profit, hacktivism, stealing state secrets, and revenge against former employers or enemies. But make no mistake, the prime motive is profit. The cost of cybercrime will top $2 trillion by 2019, according to Juniper Research.
-
How Can Basic Security Knowledge Help Any Career?
“Within any role in the organization, learning about security can help an individual understand the risks and make informed decisions for their key stakeholders,” says Pavi Ramamurthy, senior manager of information security at LinkedIn.
Like what, you ask? Here are a few of Ramamurthy’s examples:
- In sales, reassure customers of an organization’s security posture.
- In corporate communications, you should assess in the context of business reputation and brand trust.
- The legal team should ensure that the right security clauses are built into supplier and customer contracts.
- Regarding HR and/or security, know what’s needed for better security awareness and training.
- Product managers should advise on good security features.
- In engineering development, make sure you develop secure code.
- Security professionals should perform reviews and quality assurance tests for functional and security verification.
- Corporate management should ensure that a good security incident response plan is in place to address any vulnerabilities.
WHATSAPP SCAM
- WHAT TO DO IF YOU HAVE BEEN TARGETED WITH FAKE SUPERMARKET VOUCHERS?
The messenger app was used to send fake vouchers to people, purporting to be from trusted chains such as Asda, Tesco, and Aldi.
A scam is a form of phishing, where fraudsters pose as reputable organizations to gain personal details.
Action Fraud, the UK’s national reporting center for fraud and cybercrime, suggests anyone who has fallen victim to this scam to report it online or call 0300 123 2040.
So far, 33 people have come forward to report falling victim to the scam, although it is unclear how many people have received the message.
- Fake WhatsApp fools Android users
- ‘We lost £300,000 through payment scam’
“If you’ve received spam from a contact, delete the message and do not click on any links or provide personal information. Tell the contact that the message they sent includes spam and point them to this WhatsApp safety page,”
7 Essential Security Awareness Topics
1. Email Security
Email is the primary method that attackers will use in order to target your organization. They may do this via targeted phishing emails, malicious URLs or even email attachments containing malware. Learning to spot these emails and distinguish them from legitimate communication is an essential skill to have.
You should educate staff about things such as email spoofing, and ensure that they are familiar with the difference between the CC and BCC email fields. More importantly, every security awareness training programme should promote the use of encrypted email.
2.Web Security
Cybercrime is rampant on the web today. There’s identity theft, organized fraud, malicious hacking and even political hacktivism. It’s now estimated that around 1 in 10 web pages contains some kind of malicious code. The primary motivation for these cybercriminals is financial – and financial crimes makes up a significant majority of the threat landscape.
We need to keep our staff up to date with the latest web-based attacks and stress the importance of keeping software up to date. We must provide education and training around how to recognize malicious web pages and spot websites which aren’t using HTTPS to process personal data securely.
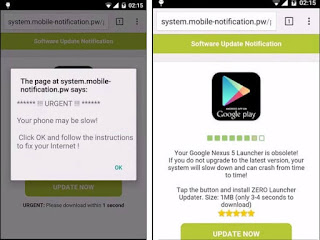
3.Mobile Security
We’re living in the information age of cloud-based platforms, where we require data on demand, and increasingly use mobile devices to enable our businesses. Field-based teams use tablets, laptops and mobile phones to access the resources they need to do their jobs and to stay in touch with their teams.
These devices store more sensitive information than ever, and in many cases utilize VPN connections back to our company headquarters. The digital perimeter used to be within the physical confines of our premises, but today it extends across the globe.
Each mobile device represents a potential point of compromise, so it’s critical to our security that we take steps to secure these devices.
4.Data Protection
The majority of developed countries have data protection legislation, which governs the protection of personal information. This legislation often covers the collection and processing, transfer and security of personal data. In many cases, the legislation also outlines the penalties for cases where data has been mishandled.
Employees should be educated on topics such as data protection legislation, industry compliance obligations, personally identifiable information, secure data destruction, data classification and breach notification procedures.
5.Environmental Security
Environmental security concerns the systems and controls that we use to restrict access to sensitive information or resources. Environmental security controls include CCTV cameras, ID cards, and access control systems.
Without physical security controls, our digital defenses could be rendered completely useless. For example, if attackers had physical access to our servers they could install a key-logger to gather password information.
6.Malware
Malware is one of the most serious threats to any organization – particularly with the introduction of new ransomware style attacks. Malware has gone from becoming a nuisance to a legitimate threat to the confidentiality, integrity, and availability of your data.
This is a particular problem when malware attacks are combined with other techniques such as phishing. Anti-spam filters are often unable to detect and prevent these emails from making it through, and anti-virus solutions are unable to detect the malware using signature-based matching.
7.Social Engineering
The single greatest threat to your security today is an attacker that’s skilled in manipulating human relationships. These attackers will attempt to gain the trust of somebody within your organization in order to obtain information or access they otherwise wouldn’t have.
Scams such as business email compromise rely upon social engineering in order to be successful. Other social engineering pretexts may call unsuspecting employees and pose at the IT department. Social engineering is the #1 method that attackers will use to bypass your expensive firewall equipment.







Pingback: Cyber Hygiene: Best Cybersecurity Practices | WebOrion™ Cyber Security and Vulnerability Assessment Services