A new ransomware family targeting Android devices spreads to other victims by sending text messages containing malicious links to the entire contact list found on already infected targets. The malware dubbed Android/Filecoder.C (FileCoder) by the ESET research team which discovered it is currently targeting devices running Android 5.1 or later.”Due to narrow targeting and flaws in both execution of the campaign and implementation of its encryption, the impact of this new ransomware is limited,” ESET’s researchers found. After the ransomware sends out this batch of malicious SMSes, it encrypts most user files on the device and requests a ransom. Due to flawed encryption, it is possible to decrypt the affected files without any assistance from the attacker,” adds ESET. Despite this, if the ransomware’s developers manage to fix their “product,” a lot of Android users could be exposed to a very dangerous and potentially highly destructive malware strain.
Due to rushing with the publication of this research – in order to warn about this threat as soon as possible – we erroneously stated that “because of the hardcoded key value that is used to encrypt the private key, it would be possible to decrypt files without paying the ransom by changing the encryption algorithm to a decryption algorithm”. However, this “hardcoded key” is an RSA-1024 public key, which can’t be easily broken, hence creating a decryptor for this particular ransomware is close to impossible. Hat tip goes to Alexey Vishnyakov from Positive Technologies who drew our attention to this inaccuracy.
After two years of decline in Android ransomware, a new family has emerged. We have seen the ransomware, detected by ESET Mobile Security as Android/Filecoder.C, distributed via various online forums. Using victims’ contact lists, it spreads further via SMS with malicious links. Due to narrow targeting and flaws in the execution of the campaign, the impact of this new ransomware is limited. However, if the operators start targeting broader groups of users, the Android/Filecoder.C ransomware could become a serious threat.
Android/Filecoder.C has been active since at least July 12th, 2019. Within the campaign we discovered, Android/Filecoder.C has been distributed via malicious posts on Reddit and the “XDA Developers” forum, a forum for Android developers. We reported the malicious activity to XDA Developers and Reddit. The posts on the XDA Developers forum were removed swiftly; the malicious Reddit profile was still up at the time of publication.
Android/Filecoder.C spreads further via SMS with malicious links, which are sent to all contacts in the victim’s contact list. After the ransomware sends out this batch of malicious SMSes, it encrypts most user files on the device and requests a ransom. Users with ESET Mobile Security receive a warning about the malicious link; should they ignore the warning and download the app, the security solution will block it.
Ransomware SMS infection vector
Spreading
FileCoder was first seen by ESET during a campaign spanning back as far as July 12, with the attackers distributing their malicious payload via posts made on Reddit and on the XDA Developers mobile software development community. While XDA removed the malicious posts after being notified, the Reddit threads were still up and going at the time ESET malware researcher Lukas Stefanko published the FileCoder malware analysis.FileCoder ‘s developers use two servers to distribute the ransomware, with malicious payloads being linked from both the malicious text messages sent to the victims’ entire contact list and from the Reddit and XDA’s forum posts.
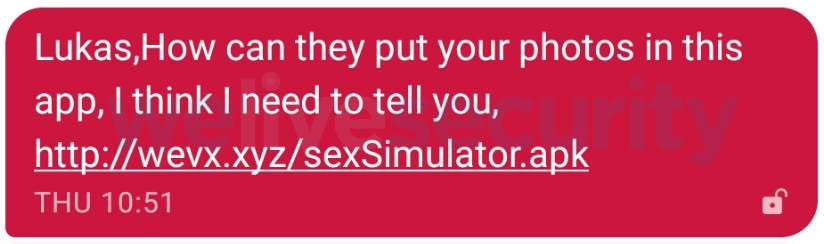
The ransomware samples are also linked to with the help of QR codes that would make it faster for mobile users to get the malicious APKs on their devices and install them on their devices. As a bait to convince potential victims to install the infected Android apps on their devices, FileCoder’s operators would say that the app “supposedly uses the potential victim’s photos.”However, the Reddit and XDA forum posts “promote” the malicious app as a free sex simulator online game which should also lower the potential targets’ guard enough to get them to download and install the ransomware-ridden app on their devices.
Functionality
As BleepingComputer found when analyzing a FileCoder sample, while being installed on a victim’s Android device, the malware will request for the following permissions:
android.permission.SET_WALLPAPER
android.permission.WRITE_EXTERNAL_STORAGE
android.permission.READ_EXTERNAL_STORAGE
android.permission.READ_CONTACTS
android.permission.RECEIVE_BOOT_COMPLETED
android.permission.SEND_SMS
android.permission.INTERNET“To maximize its reach, the ransomware has the 42 language versions of the message template […]. Before sending the messages, it chooses the version that fits the victim device’s language setting. To personalize these messages, the malware prepends the contact’s name to them,” ESET found.
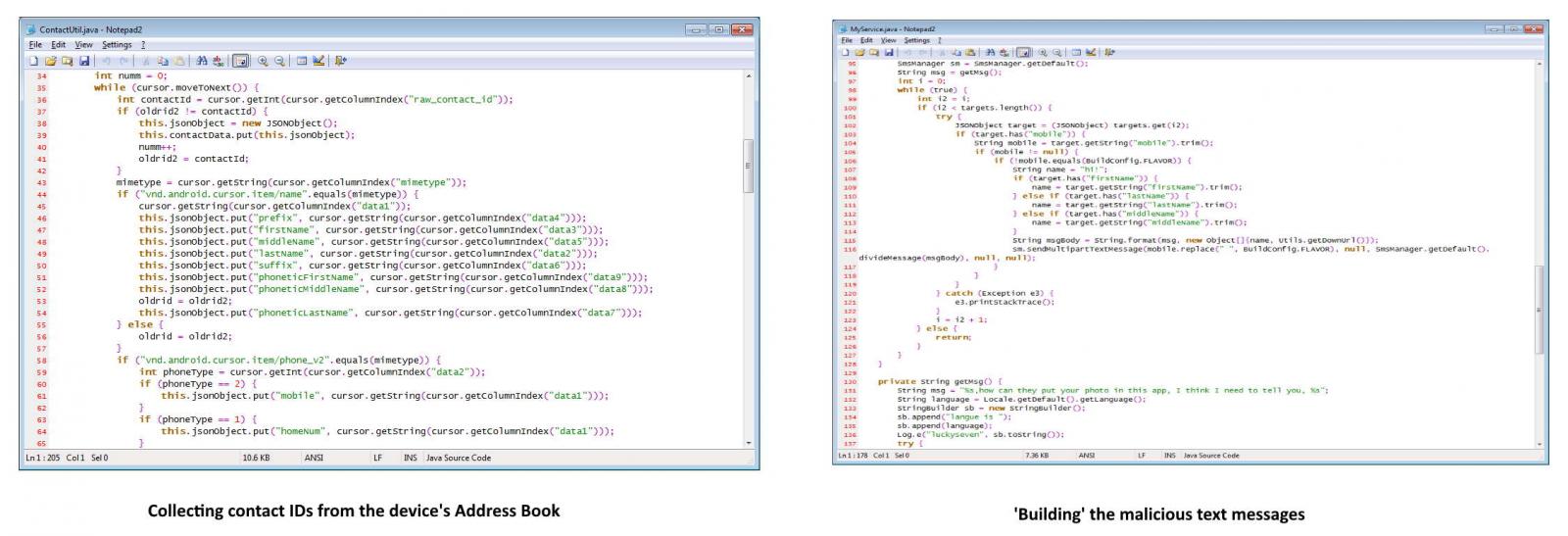
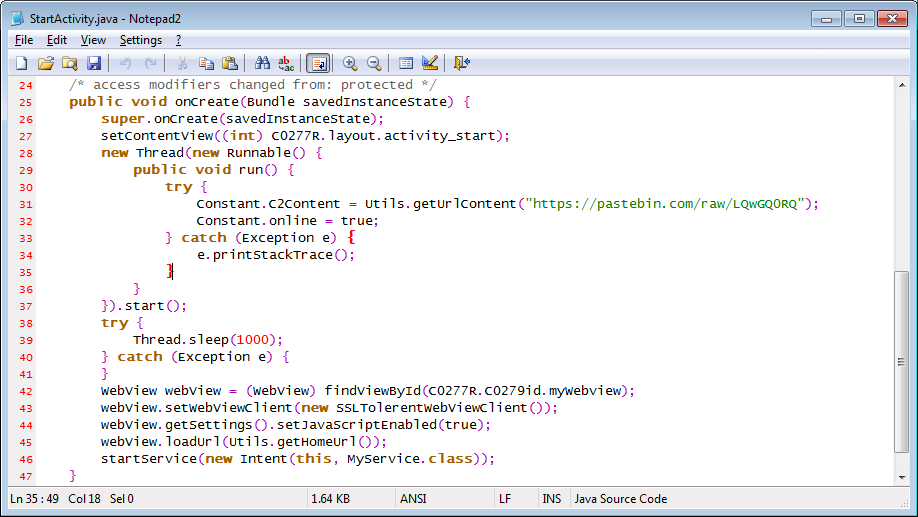
The FileCoder ransomware asks its victims for a Bitcoin ransomware, with the Bitcoin addresses and the command-and-control (C2) server being hardcoded within the malware’s source code but with the option of new addresses being sent via the Pastebin service.
“The ransomware also leaves files unencrypted if the file extension is “.zip” or “.rar” and the file size is over 51,200 KB/50 MB, and “.jpeg”, “.jpg” and “.png” files with a file size less than 150 KB,” adds ESET.
The malware will encrypt a weird mix of Android-specific file types as well as a weird combination of unrelated document types, with the ESET research team concluding that “the list has been copied from the notorious WannaCryptor aka WannaCry ransomware.”
File Coder C2 servers still active
After all the files get locked by the malware, it will display the ransom note, detailing the number of encrypted files and the amount of time the victim has to pay for the cost of the decryption key — the ransom amounts range between $94 and $188.While the ransom note says that the data will be lost if the ransom is not paid within three days, “there is nothing in the ransomware’s code to support the claim that the affected data will be lost after 72 hours.”
Unlike most other Android ransomware strains, FileCoder will not lock the victims’ screens and will allow them to continue to use their devices, depending only on the fact that its targets will want their files decrypted as soon as possible.FileCoder encrypts files using new AES keys for each of the files it locks, employing a pair of public and private keys, with the latter being encrypted with the help of the RSA algorithm.
However, because the ransomware’s developers have hard coded the value used to encrypt the private key within the malware’s code, victims could decrypt their data without paying the ransom.”All that is needed is the UserID provided by the ransomware, and the ransomware’s APK file in case its authors change the hardcoded key value,” found the ESET researchers.
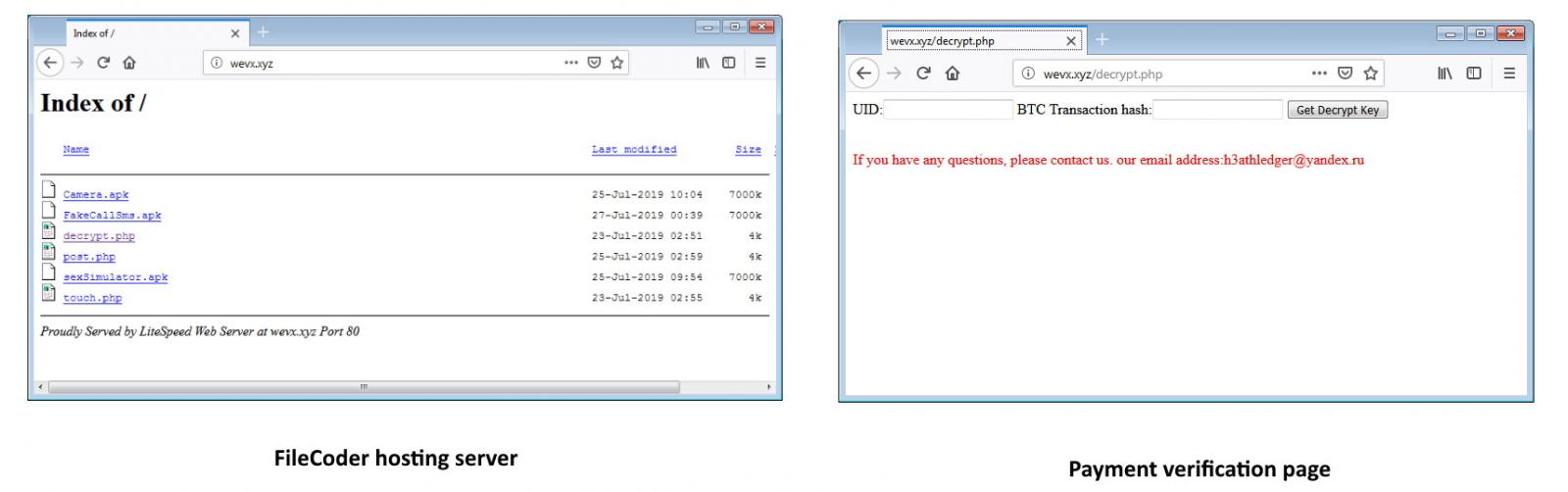
At the time this story was published, the servers used by FileCoder’s authors were still online, with the ransom payment verification page also being available via one of the files hosted on the malware’s C2 servers. The payment verification page also provides the victims with a ‘support email’ designed to allow them to ask for help if facing any issues: “If you have any questions, please contact us. our email address:h3athledger@yandex.ru”.
How to stay safe
- First of all, keep your devices up to date, ideally set them to patch and update automatically, so that you stay protected even if you’re not among the most security-savvy users.
- If possible, stick with Google Play or other reputable app stores. These markets might not be completely free from malicious apps, but you have a fair chance of avoiding them.
- Prior to installing any app, check its ratings and reviews. Focus on the negative ones, as they often come from legitimate users, while positive feedback is often crafted by the attackers.
- Focus on the permissions requested by the app. If they seem inadequate for the app’s functions, avoid downloading the app.
- Use a reputable mobile security solution to protect your device.
